Cybersecurity meets automotive business


Table of contents
Schedule a consultation with automotive software experts
Contact usThe automotive industry is well known for its security standards regarding the road safety of vehicles. All processes regarding vehicle development - from drawing board to sales - were standardized and refined over the years. Both internal tests, as well as globally renowned companies like NHTSA or EuroNCAP, are working hard on making the vehicle safe in all road conditions - for both passengers and other participants of road traffic.
ISO/SAE 21434 - new automotive cybersecurity standard
Safety engineering is currently an important part of automotive engineering and safety standards, for example, ISO 26262 and IEC 61508. Techniques regarding safety assessment, like FTA (Fault Tree Analysis), or FMEA (Failure Mode and Effects Analysis) are also standardized and integrated into the vehicle development lifecycle.
With the advanced driver assistance systems starting to be a commodity, the set of tests started to quickly expand adapting to the market situation. Currently, EuroNCAP takes into account automatic emergency braking systems, lane assist, speed assistance, or adaptive cruise control. The overall security rating of the car highly depends on modern systems.
But the security is not limited to crash tests and driver safety. In parallel to the new ADAS systems, the connected car concept, remote access, and in general, vehicle connectivity moved forward. Secure access to the car does not only mean car keys but also network access and defense against cybersecurity threats.
And the threat is real. 6 years ago, in 2015, two security researchers hacked Jeep Cherokee driving 70mph on a highway by effectively disabling its breaks , changing the climate control and the infotainment screen display. The zero-day exploit allowing that is now fixed, but the situation immediately caught the public eye and changed the OEMs mindset from “minor, unrealistic possibility” to “very important topic”.
There was no common standard though. OEMs, Tier1s, and automotive software development companies worked hard to make sure this kind of situation never happens again.
A few years later other hackers proved that the first generation of Tesla Autopilot could be tricked to accelerate over the speed limit by only slightly changing the speed limit road sign. As a result, discussion about software-defined vehicles cybersecurity sparked again.
All of these resulted in the definition of the new standard called ISO 21434 “Road vehicles — cybersecurity engineering . The work started last year, but currently, it’s at the “Approval” phase, so we can quickly go through the most important topics it tackles.
In general, the new norm provides guidelines for including cybersecurity activities into processes through the whole vehicle lifecycle. The entire document structure is visualized below:
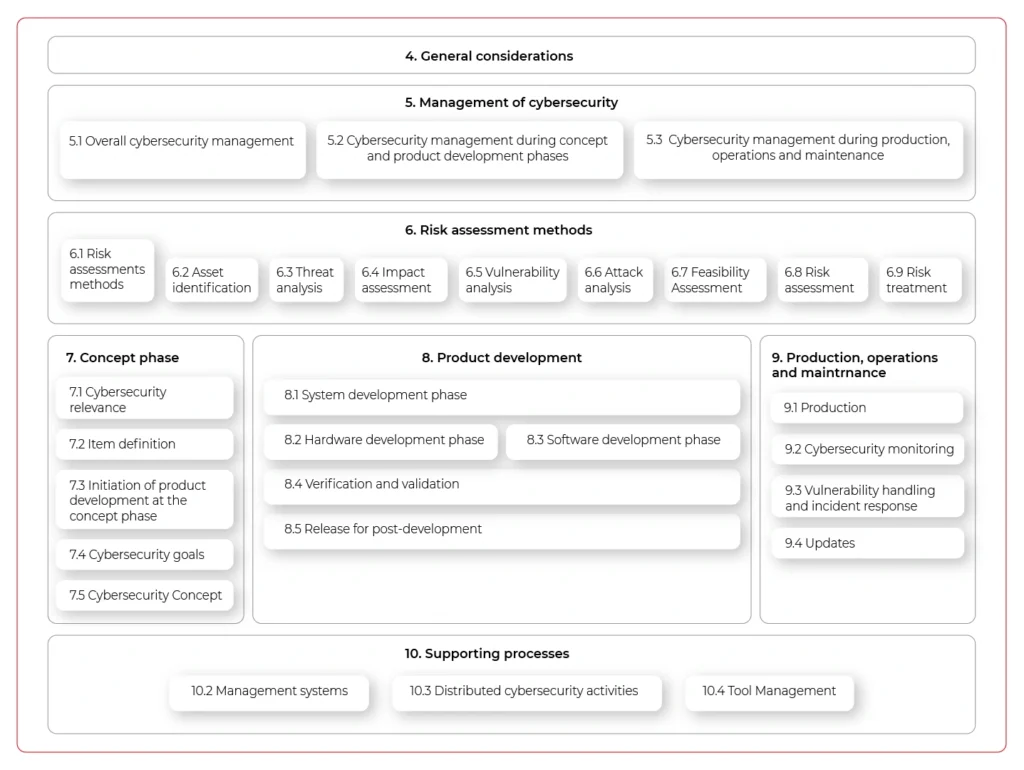
The important aspect of the new standard is that it does not only handle vehicle production but all activities until the vehicle is decommissioned - including incident response or software updates. It does not just focus on singular activities but highly encourages the continuous improvement of internal processes and standards.
The document also lists the best practices regarding cybersecurity design:
- Principle of least privilege
- Authentication and authorization
- Audit
- E2E security
- Architectural Trust Levels
- Segregation of interfaces
- Protection of Maintainability during service
- Testability during development (test interface) and operations10.
- Security by default
The requirements do not end on the architectural and design level. They can go as low as the hardware (identification of security-related elements, documentation, and verification for being safe, as they are potential entry points for hackers), and source code, where specific principles are also listed:
- The correct order of execution for subprograms and functions
- Interfaces consistency
- Data flow and control flow corrections
- Simplicity, readability, comprehensibility
- Robustness, verifiability, and suitability for modifications
The standard documentation is comprehensive, although clearly visible in the provided examples rather abstract and not specific to any programming languages, frameworks, and tools. There are recommendations, but it’s not intended to answer all questions, rather give a basis for further development. While not a panacea to all cybersecurity problems of the industry, we are now at the point when we need standardization and common ground for handling security threats in-vehicle software and connectivity, and the new ISO 21434 is a great start.

Data powertrain in automotive: Complete end-to-end solution
We power your entire data journey, from signals to solutions
Check related articles
Read our blog and stay informed about the industry's latest trends and solutions.
How new mobility services change the automotive industry
The automotive industry is changing right before our very eyes. Today, services based on the CASE model are looming on the horizon. They are capturing an increasing market share and gaining more and more each year in total dollar value. What's in store for the automotive sector and how automotive enterprises can seize these opportunities?
New mobility services are emerging rapidly
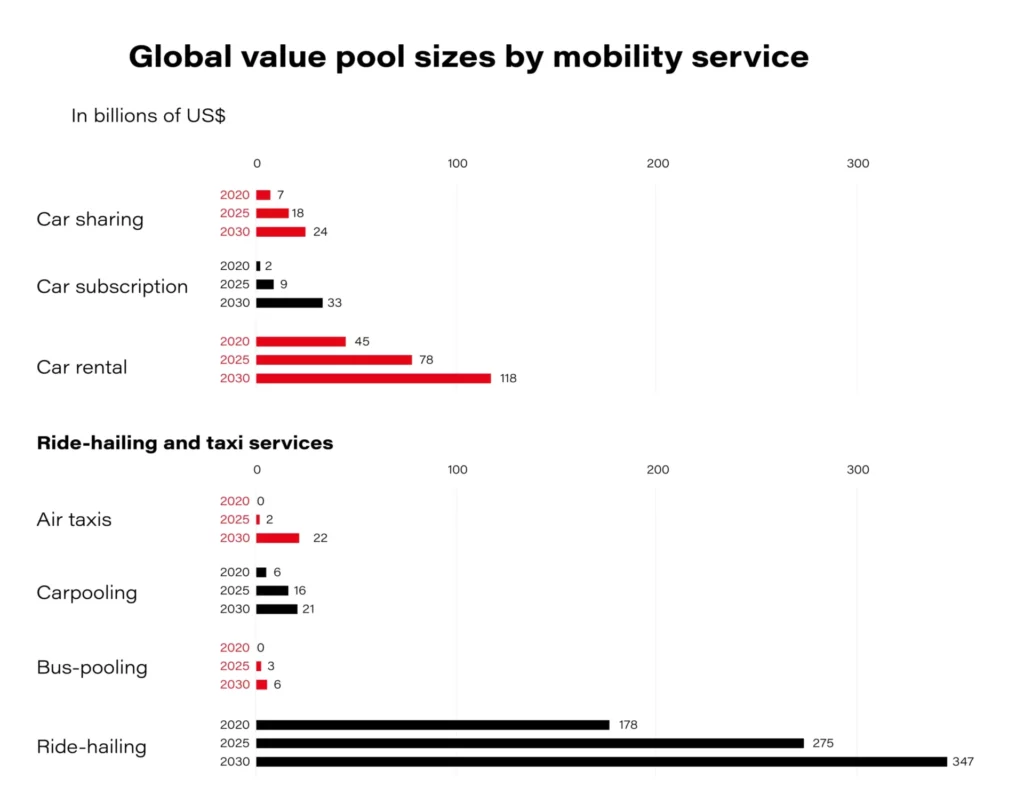
By 2030, over 30 percent of the projected increase in vehicle sales due to urbanization and macroeconomic growth will be unlikely to happen owing to the shared mobility expansion.
In China, the European Union, and the United States, which are countries supporting shared mobility solutions , the mobility market could reach 28 percent annual growth from 2015 to 2030 . Of course- this would be the most optimistic scenario. FutureBridge specialists expect the shared mobility market to grow significantly over the next five to seven years at a CAGR of 16 percent from 2018, reaching 180 billion dollars by 2025 . How can the growing demand for new mobility services be explained?
On the one hand, the automotive industry deals with changing consumer preferences . One travels by car covering shorter distances, but much more frequently. And it doesn’t have to be by car at all, as new means of transportation are becoming more accessible.
On the other hand, soaring car prices (though cars lose their value a few months after the purchase) prompt us to search for other, cheaper alternatives that provide optimal driving comfort anyway.
How will companies relying on the traditional car ownership model respond to this trend? They will provide new services such as substitution models, in which, for a once-off monthly payment, you can have a new car with insurance, maintenance, roadside assistance, etc. Subscriptions will soon account for about 15% of new car sales and should have risen to 25% by 2025. In this context, new mobility in the form of rental and ride-sharing services, which are also part of the transformation on the roads, also becomes significant.
The third thing is growing technology, based on the CASE model(Connectivity, Autonomous driving, Shared mobility, Electrification,) that empowers the development of new mobility services on an unprecedented scale. According to Microsoft experts, by 2030 virtually all new cars will have been connected devices, functioning as data centers on wheels.
6 leading new mobility services
Carsharing
A short-term car rental model that allows users to choose a vehicle and pick-up/drop-off location. Users can determine vehicles and flexible rent times. Operators gain high ROI with high utilization and minimal staffing.
Examples: citybee, E-VAI, fetch
Ride-hailing
A form of cab rental in which the drivers are usually contractors using their private vehicles rather than direct employees. The user has immediate availability and payment is handled through the operator. The benefits are also the ability to track and monitor journeys. For operators instead, traditional fleet costs must be handled by the drivers. It’s an easily scalable service.
Examples: Uber, Lyft, Bolt, marcel, OLA
P2P Sharing
this service allows vehicle owners to rent their vehicles when they are not currently in use. BMW-run ReachNow is piloting a version of this type of service, which allows Mini owners to offer their currently unused vehicles for rent. The benefits for users are the lower costs than traditional vehicle rental. Meanwhile, the operator has no fleet to manage and gets access to an easily scalable model of business.
Examples: HoppyGo, SnappCar
Carpooling
Allows users to join an already scheduled trip. The operating company acts as an "intermediary" through which rides can be announced and joined. Carpooling can apply both to people taking a trip alone and to those who want to share rides to reduce the total cost of the trip for a single passenger. It’s a cheap and environmentally friendly service. What is more, the operator has a higher margin per ride and no fleet to manage.
Examples: BlaBlaCar, GoMore, liftshare
Car rental
The evolution of the traditional car rental by the day, allowing users to rent cars for different periods without the traditional hassle associated with this type of service. From the user's point of view, such new services enable an easier and quicker process of vehicle rental. Also, it’s possible to choose a vehicle before finalizing the rental. In turn, the operator has less staffing than a traditional rental and can utilize already existing fleets.
Examples: Audi Silvercar, Hertz, Sixt, PORSCHE DRIVE, UBEEQO
Multimodal
An integrator of public transport mobility services, as well as other modes of transportation, such as public transportation, rail networks, and even cabs. The goal of such services is to get people from their starting point to their destination in the fastest, cheapest, or most efficient way, depending on individual needs. In this model, the operator gets access to additional potential users and has relatively low costs of deployment due to a lack of physical assets.
Examples: FREE2MOVE, whim, Google Maps
Which new mobility services are growing the fastest?
Of the 55 providers of the aforementioned new mobility services operating in European countries, the most popular are those in the area of carsharing (51%) . The second most popular are car rental services (20%) , followed by P2P sharing (13%) .
In terms of ownership, most new mobility services were OEM owned (over 36%), although many of them were independent (over 38%). Also included were OEM invested services (31%).
Technologies and functionalities fueling the development of new mobility services
Mobility services are based on advanced software that uses, at least, the Internet of Things, to transfer data from the vehicle to the cloud. Then the individual information is available on the user's mobile application.
For services based on unmanned vehicle rental, modern security features have been considered when it comes to opening and closing the car.
With a view to minimizing possible problems, the developers of digital new mobility services are also introducing a fault reporting option.
Below is a selection of the most common functionalities and technologies in detail for each new mobility service in Europe.
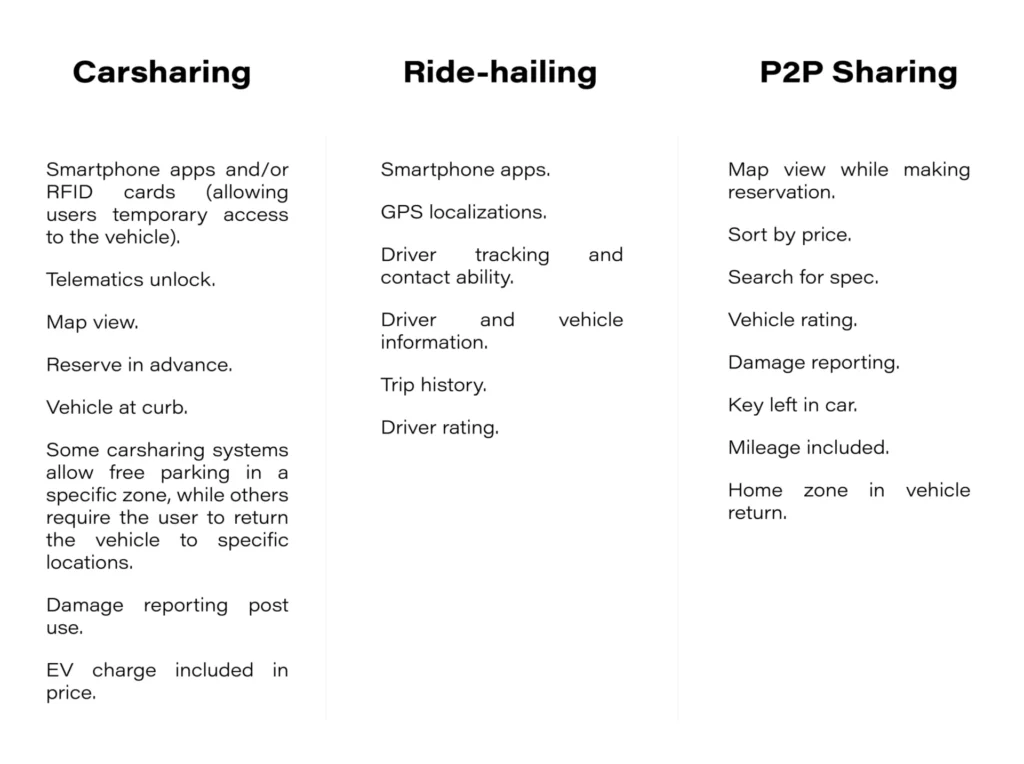
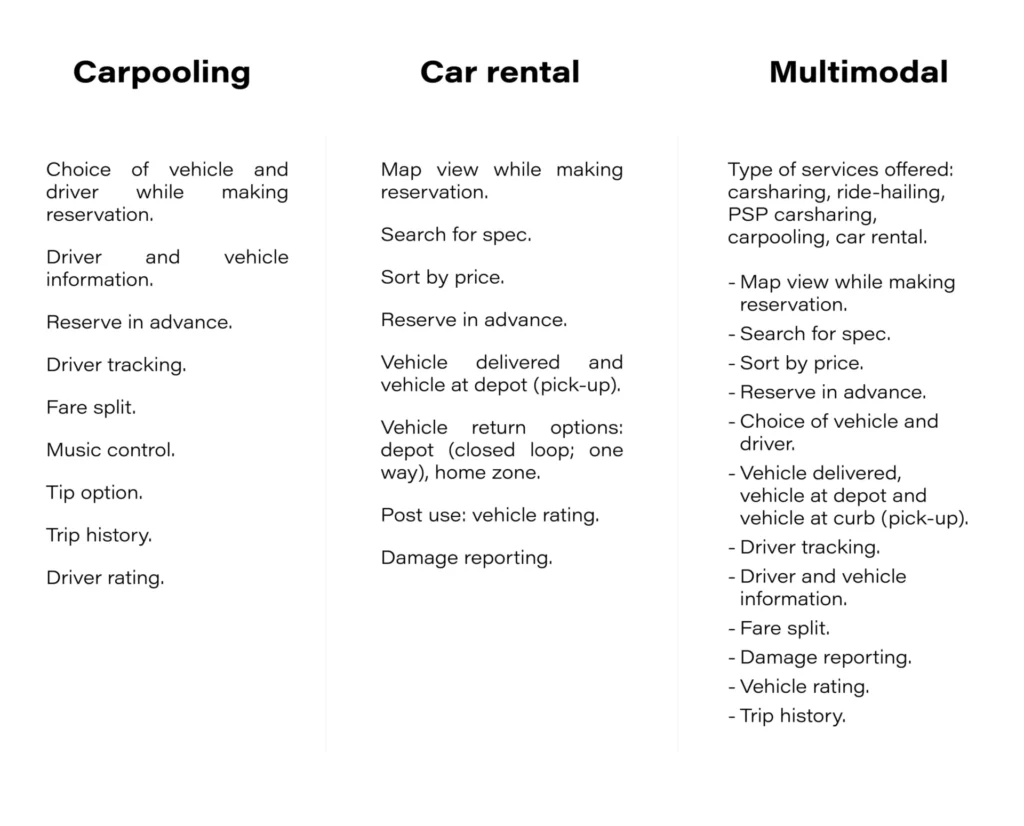
All of these and other options provide guidance and a certain pattern of behavior for future developing OEMs.
Key factors crucial for the development of new mobility services
CASE trends provide new opportunities for the vehicles of the future. However, the interrelationships between software, in-car sensors, and electronic systems require a huge amount of resources , especially when we are talking about reliable operations that translate into a competitive advantage of new mobility services and popularity among potential users.
Therefore, if you want to develop in this area, consider at least these few factors.
- Cybersecurity . In addition to creating huge amounts of code, what also matters is that your user data tracking processes comply with the standards and regulations that apply in your geographic region.
- Careful listening to user needs. In order to compete with technology start-ups, OEMs should focus on innovative digital solutions oriented towards actual consumer expectations . What matters is flexibility, when it comes to the portfolio of functionalities.
- Certainly, emotion is a factor that must be taken into account. Solution providers should care about providing unique experiences and sensations that will make the user eager to re-use a particular service, and in the process, spread it to their community.
- Flexibility and scalability . You need to be prepared not only to meet the changing expectations of customers who come in with feedback but also to expand functionality to include those that competitors already have (or to offer completely innovative solutions).
- Being ready to expand the offering . For example, with new types of vehicles: not only internal combustion but also hybrid, electric; not only cars but also city scooters, etc.
If you want to deal with the challenges that come with developing new mobility services and are considering the above and other growth factors, contact Grape Up. We can help you expand your business in terms of features and values appreciated by today's conscious consumers.
How predictive maintenance changes the automotive industry
Ever since Henry Ford implemented the first production line and launched mass production of the Ford Model T, the automotive industry has been on the constant lookout for ways to boost performance. This aspect has become even more relevant today, given the constant market and social unrest. Coming to rescue supply chain management and product lifecycle optimization is predictive maintenance. Not only OEMs, but the entire automotive industry: insurers, car rental companies and vehicle owners are benefiting from the implementation of this technology.
Predictive maintenance explained
Predictive maintenance is an advanced maintenance approach that utilizes data science and predictive analytics to anticipate when equipment or machinery requires maintenance before it faces a breakdown.
The primary aim is to schedule maintenance at optimal times, considering convenience and cost-effectiveness while maximizing the equipment's longevity. By identifying potential issues before they become critical, predictive maintenance significantly reduces the likelihood of equipment breakdowns.
Various types of maintenance strategies are employed in different industries:
- Reactive Maintenance: Also known as "run-to-failure," this method involves waiting for equipment to fail before conducting maintenance. Therefore, unscheduled downtime and higher repair costs may occur.
- Periodic Maintenance : This approach entails performing maintenance tasks at regular intervals, regardless of the equipment's condition. It helps prevent unexpected breakdowns but may lead to unnecessary maintenance if done too frequently.
- Smart Maintenance : Smart maintenance utilizes advanced technologies like IoT devices and sensors to monitor equipment in real-time and identify anomalies or potential failures.
- Condition-Based Maintenance : This strategy relies on monitoring the equipment's condition while it is in operation. Maintenance is only carried out when data indicates a decline in performance or a deviation from normal parameters, optimizing maintenance schedules and reducing unnecessary work.
- Predictive Maintenance : The most advanced type of maintenance uses real-time operational data and predictive analytics to forecast when maintenance is required. It aims to schedule maintenance before equipment failure occurs based on data-driven predictions, thus minimizing downtime, reducing costs, and prolonging equipment lifespan.
Predictive maintenance employs various techniques, such as vibration analysis, acoustic monitoring, infrared technology, oil analysis, and motor circuit analysis. These methods enable continuous equipment condition monitoring and early detection of potential failures, facilitating timely maintenance interventions.
Differentiation between predictive maintenance and preventive maintenance
Predictive maintenance hinges on the real-time condition of assets and is implemented only when the need arises. Its purpose is to anticipate potential failures by monitoring assets while they are actively operational. Unlike preventive maintenance , this approach is rooted in the current operational state of an asset rather than statistical analysis and predetermined schedules.
Essential steps in creating a predictive maintenance solution
Predictive maintenance solutions utilize a combination of sensors, artificial intelligence, and data science to optimize equipment maintenance.
The development of such solutions varies depending on equipment, environment, process, and organization, leading to diverse perspectives and technologies guiding their creation. However, there are steps common to every project: data collection and analysis, model development and deployment, as well as continuous improvement.
Here is a step-by-step process of how solutions are developed in the automotive industry :
- Data Collection : Relevant data is collected from sensors, equipment logs, vehicle diagnostics, telemetry, and other sources. This data includes information about the performance, condition, and behavior of the vehicles, such as engine temperature, fuel consumption, mileage, and more. Telematics systems can provide real-time data on vehicle location, speed, and usage patterns, while maintenance logs record historical maintenance activities, repairs, and part replacements.
- Data Preprocessing : The collected data is organized, and prepared for analysis. Data preprocessing involves cleaning the data by removing outliers or erroneous values, handling missing values through imputation or interpolation, and converting the data into a suitable format for analysis.
- Feature Engineering : Important features or variables that can provide insights into the health and performance of the vehicles are selected from the collected data. These features can include engine vibration, temperature, fuel consumption, mileage, and more. Feature selection step involves identifying the most relevant features that have a strong correlation with the target variable (e.g., equipment failure). It helps to reduce the dimensionality of the data and improve the model's efficiency and interpretability. Later, selected features are transformed to make them more suitable for modelling. The process may include techniques such as logarithmic or exponential transformations, scaling, or encoding categorical variables.
- Model Development : Machine learning algorithms are applied to the selected features to develop predictive models. These models learn from historical data and identify patterns and relationships between various factors and equipment failures. The algorithms used can include regression, decision trees, random forests, neural networks, and more.
- Model Training and Validation : The developed models are trained using historical data and validated to ensure their accuracy and performance. This involves splitting the data into training and testing sets, evaluating the model's performance metrics, and fine-tuning the model if necessary.
- Deployment and Monitoring : The trained models are deployed into the predictive maintenance system, which continuously monitors real-time data from sensors and other sources. Telematics systems are used to collect GPS and vehicle-specific data, which it transmits through different methods (cellular network, satellite communication, 4G mobile data, GPRS) to the central server. The system detects anomalies, recognizes patterns, and provides insights into the health of the vehicles. It can alert maintenance teams when potential issues are detected.
- Continuous Improvement : The predictive maintenance solution is continuously improved by collecting feedback, monitoring its performance, and updating the models and algorithms as new data becomes available.
Most common problems in deploying predictive maintenance solutions
Implementing predictive maintenance solutions in a fleet of vehicles or in a vehicle factory is a process that requires time, consistency and prior testing. Among the main challenges of rolling out this technology, the following aspects in particular are noteworthy.
Data integration
Integrating data from many sources is a significant barrier to implementing predictive maintenance solutions. To accomplish this with a minimum delay and maximum security, it is necessary to streamline the transfer of data from machines to ERP systems. To collect, store, and analyze data from many sources, businesses must have the proper infrastructure in place.
Insufficient data
Lack of data is a major hindrance to implementing predictive maintenance systems. Large amounts of information are needed to develop reliable models for predictive maintenance. Inadequate information might result in inaccurate models, which in turn can cause costly consequences like premature equipment breakdowns or maintenance.
To get over this difficulty, businesses should collect plenty of data for use in developing reliable models. They should also check that the data is relevant to the monitored machinery and of high quality. Businesses can utilize digital twins, or digital representations of physical assets, to mimic the operation of machinery and collect data for use in predictive maintenance systems.
Process complexity
Transitioning from preventive to predictive maintenance is complex and time-intensive. It requires comprehensive steps beyond technology, including assembling a skilled team and managing upfront costs. Without qualified experts versed in software and process intricacies, project success is doubtful.
High costs
The implementation of predictive maintenance programs comes with substantial costs. These upfront expenses pose challenges, including the need to invest in specialized sensors for data collection, procure effective data analysis tools capable of managing complexity, and possibly hire or train personnel with technical expertise.
To address these hurdles, collaboration with specialized vendors and the utilization of cloud-based solutions can prove cost-effective. Additionally, digital twin technology offers a way to simulate equipment behavior and minimize reliance on physical sensors, potentially reducing overall expenses.
Privacy and security issues
The implementation of predictive maintenance involves extensive data collection and analysis, which can give rise to privacy concerns. Companies must adhere to applicable data protection laws and regulations, and establish proper protocols to safeguard the privacy of both customers and employees. Even though predictive maintenance data may be anonymized and not directly linked to specific individuals, it still necessitates robust security measures, since preventing data breaches and unauthorized access to vital company information is crucial for overall success.
What Are the Benefits of Predictive Maintenance?
Life cycle optimization, stock management, or even recycling management - in each of these fields predictive maintenance can bring substantial benefits. And this is not only for OEMs but also for fleet operators, transportation or logistics companies. And even for the end user.
Below we list the key benefits of implementing predictive maintenance in an automotive-related company:
- Extended lifespan: Predictive maintenance technology detects early signs of wear and potential malfunctions in-vehicle components such as engines, transmissions, and brakes. By addressing these issues proactively, vehicles experience fewer major breakdowns and continue to operate efficiently over a longer period.
- Cost savings: By addressing issues at an early stage, automotive companies can avoid expensive breakdowns and prevent further damage. This proactive approach not only reduces the need for costly replacement parts but also minimizes the labor and operational costs associated with major repairs, resulting in significant long-term cost savings.
- Minimized downtime : Through continuous monitoring and analysis, predictive maintenance predicts when maintenance or repairs are needed and schedules them during planned downtime. This minimizes the likelihood of unexpected breakdowns that can disrupt operations and lead to extended periods of vehicle inactivity. By strategically timing maintenance activities, vehicles spend more time on the road.
- Increased efficiency : Any iissues are detected early, enabling timely corrective actions. This proactive approach leads to improved fuel economy, reduced emissions, and overall enhanced efficiency. Vehicles operate at their peak performance, contributing to a more sustainable and environmentally friendly fleet.
- Enhanced security: Constant monitoring for abnormal vibrations, temperature variations, and fluid leaks ensures that potential issues compromising vehicle safety and security are detected promptly. By addressing these concerns before they escalate, predictive maintenance contributes to ensuring the security of both the vehicle and its occupants. This feature is particularly valuable in critical applications where reliable vehicle performance is paramount, such as emergency response scenarios.
- Avoiding over-maintenance : If you over-maintain corporate resources, it can have the same negative consequences as when failing to maintain them on time. With predictive maintenance, you can focus on maintaining crucial resources at the best possible time and with the best possible results.
- Compliance with required standards and regulations : Laws and regulations related to vehicle production are constantly evolving and pushing OEMs to make numerous production changes (e.g. the legislation related to EV production). Predictive maintenance allows you to better suit the new expectations of legislators and monitor the points of production that are most dependent on the legal context.
- Easier management of parts and materials : As connected cars diagnostic systems become more sophisticated, drivers have the option to make small repairs sooner and keep their vehicles in a better condition. All this means that OEMs and licensed repair shops need fewer parts and can better manage supply chains.
Predictive maintenance clearly is not a one-size-fits-all solution for all sectors. Notably, it will work well for high production volumes and short lead times and anywhere you need to ensure reliability, security and convenience.
The automotive industry is a perfect fit for this model. As shown in the examples featured in the second part of the article, the top players in the market are tapping into this technology.
According to Techsci Research , “ The global predictive maintenance market was valued at USD 4.270 billion in 2020 and is projected to grow around USD 22.429 billion by 2026”.
REPAIR Act and State Laws: What automotive OEMs must prepare for
Right to Repair is becoming a key issue in the U.S., with the REPAIR Act (H.R. 906) at the center. This proposed federal law would require OEMs to give vehicle owners and independent repair shops access to vehicle-generated data and critical repair tools.
The goal? Protect consumer choice and promote fair competition in the automotive repair market, preventing manufacturers from monopolizing repairs.
For OEMs, it means growing pressure to open up data and tools that were once tightly controlled. The Act could fundamentally change how repairs are managed , forcing companies to rethink their business models to avoid risks and stay competitive.
We’ll walk you through the REPAIR Act’s key provisions and practical steps automotive OEMs can take to adapt early and avoid compliance risks.
What’s inside the REPAIR Act (H.R. 906)
The REPAIR Act (H.R. 906), also known as the Right to Equitable and Professional Auto Industry Repair Act, aims to give consumers and independent repair shops access to vehicle data, tools, and parts that are crucial for repairs and maintenance.
Its goal is to level the playing field between manufacturers and independent repairers while protecting consumer choice. This could mean significant changes in how OEMs manage vehicle data and repair services.
REPAIR Act timeline – where are we now
The REPAIR Act (H.R. 906) was introduced in February 2023 and forwarded to the full committee in November 2023.

As of January 3, 2025, the bill has not moved beyond the full committee stage and was marked "dead" because the 118th Congress ended before its passage. But the message remains clear - Right to Repair isn’t going away. The growing momentum behind repair access and data rights is reshaping the conversation.
REPAIR Act provisions
Which obligations for manufacturers are covered by the Repair Act?
1) Access to vehicle-generated data
- Direct data access: OEMs would be required to provide vehicle owners and their repairers with real-time, wireless access to vehicle-generated data. This includes diagnostics, service, and operational data.
- Standardized access platform: OEMs must develop a common platform for accessing telematics data to provide consistent and easy access across all vehicle models.
2) Standardized repair information and tools
- Fair access: Critical repair manuals, tools, software, and other resources must be made available to consumers and independent repair shops at fair and reasonable costs.
- No barriers: OEMs cannot restrict access to essential repair information. The aim is to prevent them from monopolizing repair services.
3) Ban on OEM part restrictions
- Aftermarket options: The Act prohibits manufacturers from requiring the use of OEM parts for non-warranty repairs. Consumers can choose aftermarket parts and independent service providers.
- Fair competition: This provision supports competition by allowing aftermarket parts manufacturers to offer compatible alternatives without interference.
4) Cybersecurity and data protection
- Security standards: The National Highway Traffic Safety Administration (NHTSA) will set standards to balance data access with cybersecurity.
- Safe access: OEMs can apply cryptographic protections for telematics systems and over-the-air (OTA) updates, provided they do not block legal access to data for independent repairers and vehicle owners.]
These provisions go beyond theory and will directly affect how OEMs handle repairs and manage data access. Even more challenging? The existing patchwork of state laws that already demand similar access makes compliance tricky.
Complex regulatory landscape: How Right to Repair influences automotive OEMs
The regulatory environment for the Right to Repair in the U.S. is becoming increasingly complex, with state-level laws already in effect and a potential nationwide federal law still pending. This evolving framework presents both immediate and long-term challenges for automotive OEMs, requiring them to navigate overlapping requirements and conflicting standards.
State-level laws: A growing patchwork
As of February 2025, several states have enacted comprehensive Right to Repair laws.
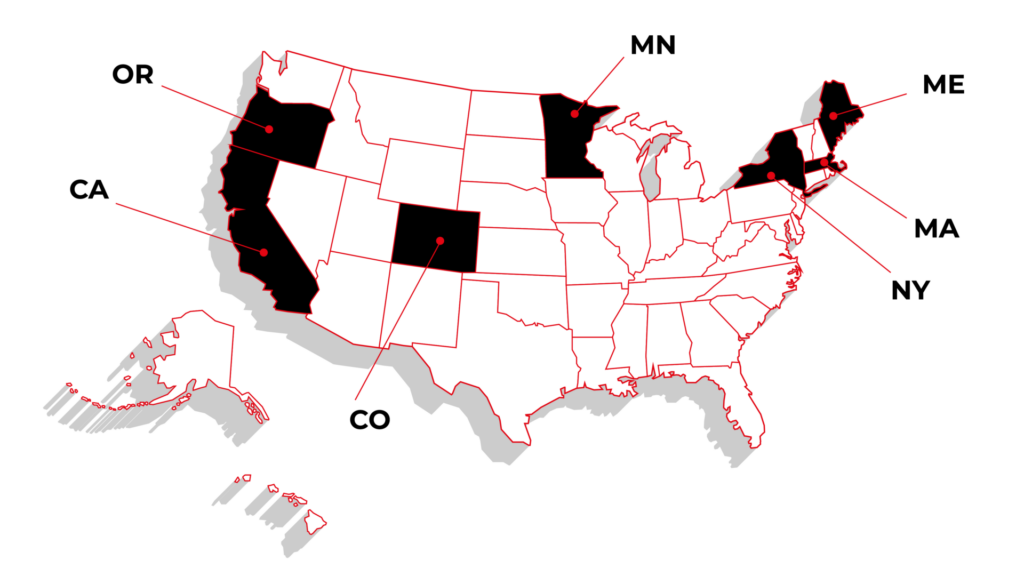
Massachusetts and Maine have laws explicitly targeting automotive manufacturers. (Automakers have sued to block the law’s implementation in Maine.)
These regulations require manufacturers to provide vehicle owners and independent repairers with access to diagnostic and repair information, as well as a standardized telematics platform.
Other states like California, Minnesota, New York, Colorado, and Oregon have focused on consumer electronics or agricultural equipment without directly impacting automotive OEMs.
However, the broader push for repair rights means automotive manufacturers cannot ignore the implications of this trend.
Additionally, as of early 2025, 20 states had active Right to Repair legislation, reflecting the momentum behind this movement. While most of these bills remain under consideration, they highlight the growing pressure for more open access to repair information and vehicle data.
Federal vs. state regulations: Compliance challenges
The pending federal REPAIR Act (H.R. 906) aims to create a unified national framework for the Right to Repair, focusing on vehicle-generated data and repair tools. However, until it becomes law, OEMs must comply with varying state laws that could contradict or go beyond future federal requirements.
Key scenarios:
- If the REPAIR Act includes a preemption clause , federal law will override conflicting state laws, providing a single set of rules for OEMs.
- If preemption is not included , OEMs will face a dual compliance burden, adhering to both federal and state-specific requirements.
This uncertainty complicates planning and increases the risk of non-compliance, making it essential for OEMs to prepare now.
Global pressures: The EU's Right to Repair mandates
The U.S. isn’t the only region focusing on the Right to Repair. European Union regulations are setting global standards for OEMs selling internationally.
- European Court of Justice Ruling (October 2023): Automotive manufacturers cannot limit repair data access under cybersecurity claims, expanding rights for independent repairers.
- EU Data Act (September 12, 2025): Requires OEMs to provide third-party access to vehicle-generated data, making open data compliance mandatory for the EU market.
For OEMs operating internationally, aligning early with these standards is a smart move. While the 2024 Right to Repair Directive doesn’t directly target vehicles, it reflects the broader trend toward increased data access and repairability.
How automotive OEMs should prepare for the Right to Repair (Even without a federal law)
Waiting is risky. Regardless of whether the REPAIR Act becomes law, preparation is key. Waiting for final outcomes could lead to costly adjustments and missed opportunities. Here’s where to start:
1. Develop a standardized vehicle data access platform
Why: Regulations require open and transparent data-sharing for diagnostics and updates. Without a standardized platform, compliance becomes difficult.
How: Focus on building a secure platform that gives vehicle owners and independent repair shops transparent access to the necessary data.
2. Provide open access to repair information and tools
Why: Some states already require OEMs to provide critical repair information and tools at fair prices. This trend is likely to expand.
How: Start creating a centralized repository for repair manuals, diagnostic tools, and other key resources.
3. Strengthen cybersecurity without restricting repair access
Why: Protecting data is critical, but legitimate repairers need safe entry points for service.
How: Develop security protocols that protect key vehicle functions without blocking legitimate access. This means securing software updates and repair-related data while allowing repairers safe entry points for diagnostics and service.
4. Improve OTA software update capabilities
Why: Having strong OTA capabilities helps comply with future regulations requiring real-time access and updates.
How: Upgrade your current OTA systems to allow secure updates and diagnostics. Include tools authorized third parties can use for updates and software repairs.
5. Transition to modular and repairable product design
Why: Designing products for easier repair reduces costs and improves compliance.
How: Shift toward using modular components that can be replaced individually. Avoid locking parts to specific manufacturers, as some states have banned this practice. Modular designs also support longer spare part availability, which many laws will require.
6. Align supply chain and warranty systems with Right-to-Repair laws
Why: Warranty terms and parts availability are common regulatory targets.
How: Make spare parts available for several years after the sale of a vehicle. Update warranty policies to allow third-party repairs and non-OEM parts without penalty.
7. Monitor regulations and adapt quickly
Why: The regulatory landscape is evolving rapidly. Staying informed about new laws and adjusting plans early will help avoid costly last-minute changes.
How: Track new laws and build flexible systems that can easily adjust as regulations change.
How an IT enabler helps OEMs prepare for Right to Repair
Managing compliance can feel overwhelming, but it doesn’t have to disrupt operations. An IT enabler helps manufacturers build systems and processes that meet regulatory demands without adding unnecessary complexity.
Here’s how:
Turning regulations into practical solutions
Right to Repair regulations vary across states and countries. An IT enabler translates these requirements into practical tools - systems for managing access to repair data, diagnostics, and tools – to make compliance more manageable.
Building the right technology
OEMs need reliable platforms that allow repairers to access diagnostic data and tools while keeping vehicle systems secure. IT experts develop scalable solutions that work across different models and markets without compromising safety.
Balancing security and access
Access to repair data must be balanced with strong security. IT solutions help protect sensitive vehicle functions while providing authorized repairers with the necessary information.
Keeping operations simple
Compliance shouldn’t add complexity. Automating key processes and streamlining workflows lets internal teams focus on core operations rather than administrative tasks.
Long-term support
Laws and standards evolve. IT partners provide continuous updates and maintenance to keep systems aligned with the latest regulations, reducing the risk of falling behind.
Delivering custom solutions
Every manufacturer has unique needs. Whether it’s updating your warranty system for third-party repairs, improving OTA update capabilities, or adapting your supply chain for spare part availability, custom solutions help you stay compliant and competitive.
At Grape Up , we help OEMs adapt to Right to Repair regulations with practical solutions and long-term support.
We have experience working with automotive, insurance, and financial enterprises, building systems that account for differences in regulations across various states.
Preparing for changes? Contact us today.
From secure diagnostics to repair information management, we provide the expertise and tools to help you stay compliant and ready for what’s next.
Interested in our services?
Reach out for tailored solutions and expert guidance.